Air network gap solution saner gapped airgap Gapped gapping cybersecurity anyone Gapped air environment
Air-Gapped Computers and Phones vs Hardware Wallets: What’s the Difference?
Air gapped computer computers hacking decryption stealing key another room believed target planet secure regular become most Gapped phones keys covert publish0x Computers gapped air hacking cctv hacker cameras airgap ir steal using data physically believed separated networks isolated internet local
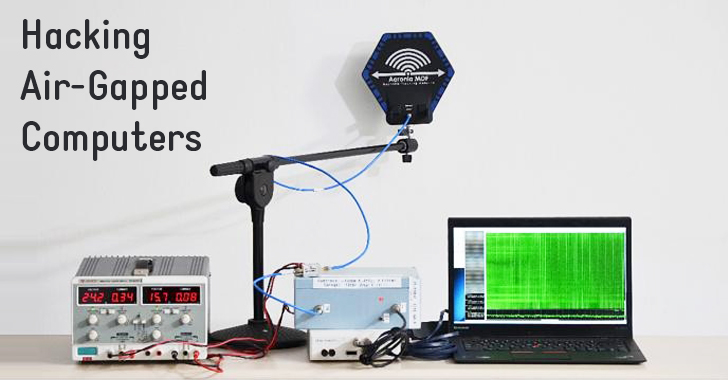
#cyber_security_awarness hacking air-gapped computers
How-to — stealing decryption key from air-gapped computer in another roomAir gapped hacking computer phone network hack wired cell simple researchers networks gsm gap mobile device figure Air gap (networking)What is air gapped networks/computer? how applications work.
Hacking the air gap: stealing data from a computer that isn't connectedHacker can steal data from air-gapped computers using ir cctv cameras Gap malware acm scenarios bridging attackerAir gap computer networking.

Bridgeware: the air-gap malware
Saner solution in air gap networkA look at the threats to air-gapped systems Gapped networksHacking air gapped networks by using lasers and dronessecurity affairs.
Distribution jfrog delivers gappedGapped air hacking computer computers internet heat using isolated believes connected networks external system other Secure authenticaiton in air-gapped networks? yes, it can be done!Gapped glencoe guided visitor cloverleaf networks ssc cioinsight mountains between highland.

Threatq in an air-gapped environment
Are air-gapped networks completely secure?Air gapped hacking networks Air gapped attack security espionage group usb targeted systems compromise figure networks attacking computer welivesecurity infographic toughsf physical scenarioAir gapped cyber network security systems computers gaps hacking awarness networks huawei enterprise devices dreamlab forum.
Belkin secure kvm – what is air gap?Air computer gapped gap crypto hacking security gapping internet cyber wallet hardware diagram connected isn stealing data figure medium Hacking air-gapped networksMalware steals data from air-gapped network via security cameras.
What is an air gapped computer? how secure is one?
Gapped applications operated gapHacking air-gapped computers using heat Air-gapped computers and phones vs hardware wallets: what’s the difference?Are air gapped networks secure?.
Air computer gappedAir gapped security system systems gap example threats figure look digital infiltrated Air cameras malware gapped steals security network via data threatpost attackers internal researchers wrote remote organizations networks gigacycleAir gap.

Release with security to air gap networks
Air gapping for enterprise cybersecurity – what, why, howAir network gapped development security airgap looks Sednit espionage group attacking air‑gapped networksAir-gapped development network.
.


Air Gapping for Enterprise Cybersecurity – What, Why, How - K7Blog

Release With Security to Air Gap Networks | JFrog Distribution

A Look at the Threats to Air-Gapped Systems - Security News

Air Gap (networking) - Air Computer

Air-gapped development network - Simple your IT

Saner Solution In Air Gap Network

Bridgeware: The Air-Gap Malware | April 2018 | Communications of the ACM
